Asset visibility and security company Armis identified connected assets posing the greatest risks to global enterprise. Armis’ new research, based on analysis from its Asset Intelligence Engine, focused on connected assets with the most attack attempts, weaponized common vulnerabilities and exposures and other high-risk factors.
Most vulnerable assets included IoT, IT, building management
The top 10 asset types with the highest number of attack attempts were distributed across IT, operational technology, the Internet of Things, the Internet of Medical Things, the Internet of Personal Things and building management systems.
SEE: Securing IoT with Microsoft Defender for IoT sensors (TechRepublic)
Armis reported that the devices with the highest number of attack attempts were:
- Engineering workstations (OT).
- Imaging workstations (IoMT).
- Media players (IoT).
- Personal computers (IT).
- Virtual machines (IT).
- Uninterruptible power supply (UPS) devices (BMS).
- Servers (IT).
- Media writers (IoMT).
- Tablets (IoPT).
- Mobile phones (IoPT).
The research reiterates findings in June this year about the most at-risk devices by the firm’s Asset Intelligence and Security Platform, which tracks over 3 billion assets according to Armis.
In that research, Armis found critical vulnerabilities in engineering workstations, supervisory control and data acquisition servers, automation servers, control system historians and programmable logic controllers, which are also the most vulnerable OT and industrial control systems.
“Malicious actors are intentionally targeting these assets because they are externally accessible, have an expansive and intricate attack surface and known weaponized CVEs,” said Tom Gol, CTO of research at Armis.
Gol said in a statement that these assets are attractive for attackers because they can wreak havoc across multiple systems.
SEE: Armis and Honeywell uncover vulnerabilities in Honeywell Systems (TechRepublic)
“Engineering workstations can be connected to all controllers in a factory, imaging workstations will collect private patient data from hospitals and UPSs can serve as an access point to critical infrastructure entities, making all of these attractive targets for malicious actors with varying agendas, like deploying ransomware or causing destruction to society in the case of nation-state attacks,” Gol said, adding that defenders should improve visibility of these assets and patch vulnerabilities (Figure A).
Figure A
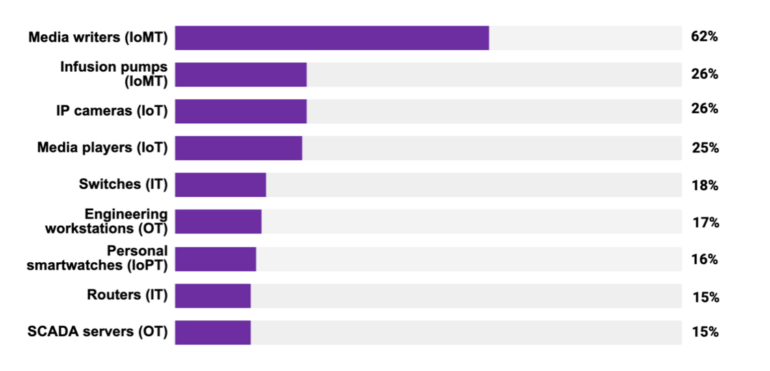
High-risk factors for common hardware and systems
The Armis researchers found a number of asset types with common high-risk factors:
- Servers and programmable logic controllers constituting end-of-life or end-of-support operating systems.
- Personal computers and the like using SMBv1, a complex and unencrypted protocol. These vulnerabilities, including EternalBlue, were exploited by WannaCry and NotPetya attacks.
- Assets with high vulnerability scores or that have had threats detected or have been flagged for unencrypted traffic or that still have the CDPwn vulnerabilities impacting network infrastructure and VoIPs.
- Half of pneumatic tube systems have an unsafe software update mechanism.
Armis said it found that 74% of organizations today still have at least one asset in their network vulnerable to EternalBlue exploited by NotPetya to gain initial access before using credential theft for privilege escalation.
“Continuing to educate global businesses about the evolving and increased risk being introduced to their attack surface through managed and unmanaged assets is a key mission of ours,” said Nadir Izrael, CTO and cofounder of Armis. “This intelligence is crucial to helping organizations defend against malicious cyberattacks. Without it, business, security and IT leaders are in the dark, vulnerable to blind spots that bad actors will seek to exploit.”