It is taking less time for organisations to detect attackers in their environment, a report by Mandiant Consulting, a part of Google Cloud, has found. This suggests that companies are strengthening their security posture.
The M-Trends 2024 report also highlighted that the top targeted industries of 2023 were financial services, business and professional services, tech, retail and hospitality, healthcare and government. This aligns with the fact that 52% of attackers were primarily motivated by financial gain, as these sectors often possess a wealth of sensitive — and therefore valuable — information.
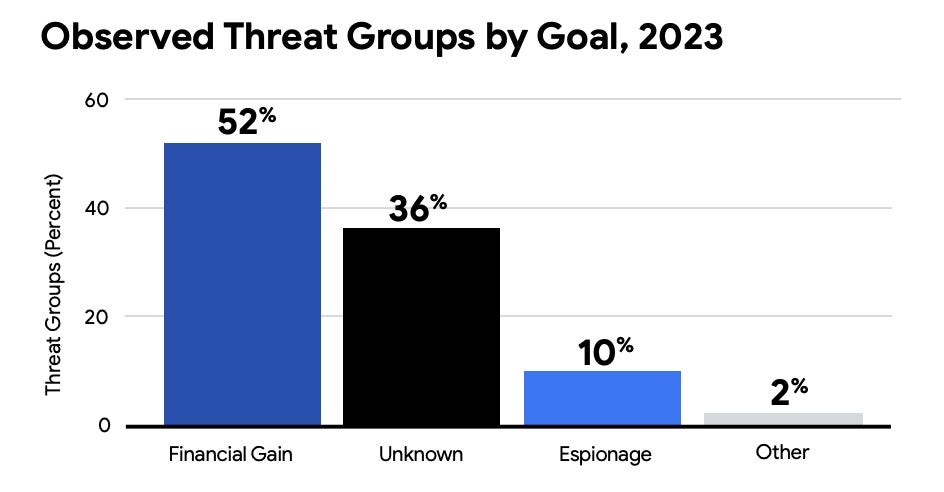
Financially-motivated activity was found to have gone up by 8% since 2022, which is partially explained by the parallel rise in ransomware and extortion cases. The most common ways that threat actors gained access to a target network were through exploits, phishing, prior compromise and stolen credentials.
Dr Jamie Collier, Mandiant Threat Intelligence Advisor Lead for Europe, told TechRepublic in an email: “Despite the focus on ransomware and extortion operations within the security community, these attacks remain effective across a range of sectors and regions. Extortion campaigns therefore remain highly profitable for cyber criminals.
“As a result, many financially-motivated groups conducting other forms of cyber crime have transitioned to extortion operations in the last five years.”
TechRepublic takes a deeper look into the top five cyber security trends of 2023 and expert recommendations highlighted by the 15th annual M-Trends report:
- Global organisations are improving their cyber defences.
- Cyber criminals have an increased focus on evasion.
- Cloud environments are being targeted more often.
- Cyber criminals are changing tactics to bypass MFA.
- Red teams are using AI and large language models.
1. Global organisations are improving their cyber defences
According to the M-Trends report, the median dwell time of global organisations decreased from 16 days in 2022 to 10 days in 2023 and is now at its lowest point in more than a decade. The dwell time is the amount of time attackers remain undetected within a target environment and indicates the strength of a business’s cyber posture. This figure suggests that companies are making meaningful improvements to their cyber security.
However, there could be another contributing factor; the average proportion of attacks due to ransomware increased to 23% in 2023 over 18% in 2022.
Dr. Collier explained to TechRepublic: “The impact of extortion operations is immediately obvious. In the event when ransomware is deployed, a victim’s systems will be encrypted and rendered unusable. Alternatively, if data is stolen, a cyber criminal will quickly be in touch to extort a victim.”
SEE: Top 7 Cybersecurity Threats for 2024
Organisations in the Asia-Pacific region saw the biggest reduction in median dwell time, with it decreasing by 24 days over the last year. Mandiant analysts link this to the fact that the majority of attacks detected were ransomware-related, and this majority was higher than any other region. Meanwhile, companies in Europe, the Middle East and Africa saw the average dwell time increase by two days. This is thought to be due to the regional data normalising following a concerted defensive effort by Mandiant in Ukraine in 2022.
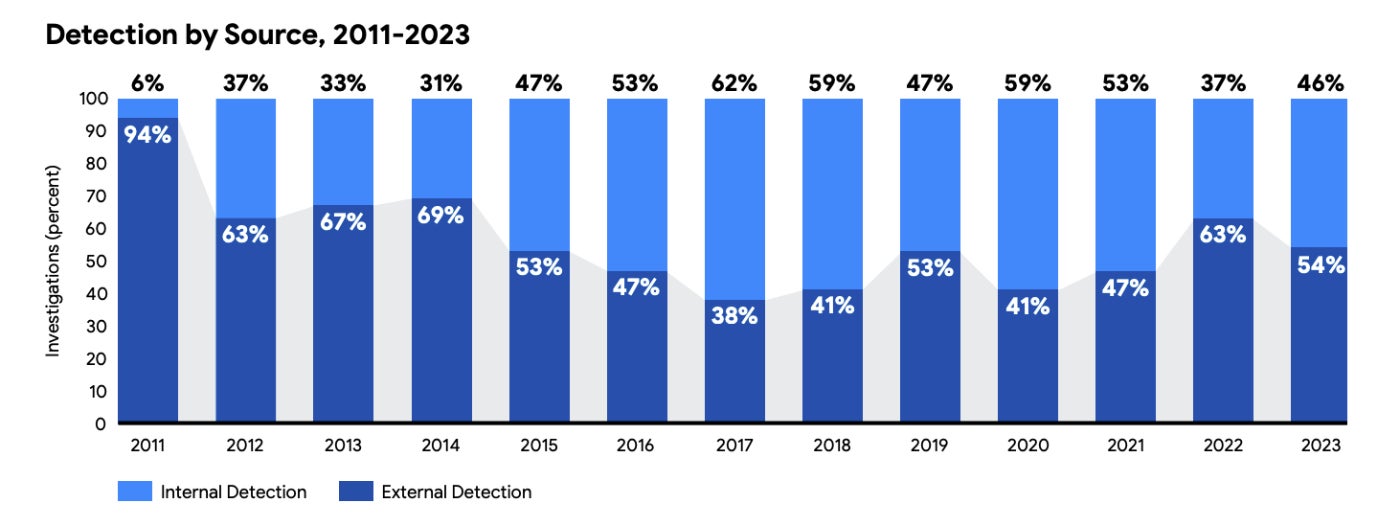
Another proof that businesses are getting better at detecting cyber threats is that Mandiant found that 46% of compromised organisations first identified evidence of compromise internally rather than by an outside entity like a law enforcement agency or cyber security company, up from 37% in 2022.
2. Cyber criminals have an increased focus on evasion
Cyber criminals are increasingly targeting edge devices, using “living off the land” techniques, and deploying zero-day exploits, suggesting a renewed focus on maintaining persistence on networks for as long as possible.
Dr. Collier told TechRepublic: “With network defenders increasingly on the lookout for extortion campaigns, evasive tactics increase the chances of a successful operation. Ransomware operations are far more effective when cyber criminals can reach the most sensitive and critical areas of a target’s network and evasive tactics help them to achieve this.”
Targeting edge devices
Edge devices typically lack endpoint detection and response (EDR) capabilities, so they are solid targets for cyber criminals looking to go under the radar. In 2023, Mandiant investigators found that the first and third most targeted vulnerabilities were related to edge devices. These were:
- CVE-2023-34362: A SQL injection vulnerability in the MOVEit file transfer application.
- CVE-2023-2868: A command injection vulnerability in physical Barracuda Email Security Gateway appliances.
The report authors wrote: “Mandiant expects that we will continue to see targeting of edge devices and platforms that traditionally lack EDR and other security solutions due to the challenges associated with discovery and investigation of compromise. Exploitation of these devices will continue to be an attractive initial access vector for Chinese espionage groups to remain undetected and maintain persistence into target environments.”
SEE: Q&A on how Dell sees security at the edge
Remote administrator tools and “living off the land” techniques
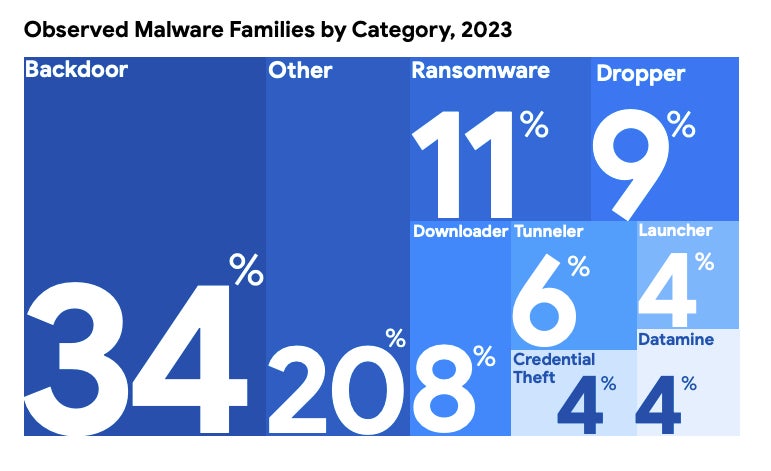
About 20% of malware families detected by Mandiant in 2023 did not fit into a typical category, which is a higher proportion than previous years. Furthermore, 8% of attacks in this “other” category involved the use of remote administration tools and other utilities. These are less likely to be flagged by default by EDR, or other security tools, which can keep the attacker undetected, and are often coupled with “living off the land” techniques.
Living off the land is the use of legitimate, pre-installed tools and software within a target environment during a cyber attack to help evade detection. This can reduce the overall complexity of the malware by allowing the attacker to weaponize existing features that have already been security tested by the organisation. It is particularly effective with edge devices because they are typically not monitored by network defenders, allowing them to remain on the network for longer.
A recent example the Mandiant researchers spotted is a backdoor named THINCRUST, which was appended into the web framework files that were responsible for providing the API interface for FortiAnalyzer and FortiManager devices. The threat actors were able to harness the native API implementation to access and send commands to THINCRUST by simply interacting with a new endpoint URL they had added.
Zero-day exploits
In 2023, Mandiant researchers tracked 97 unique zero-day vulnerabilities exploited in the wild, representing a more than 50% growth in zero-day usage over 2022. The zero-days were exploited by espionage groups and financially-motivated attackers looking to steal valuable data to turn a profit.
The report’s authors anticipate the number of identified zero-day vulnerabilities and exploits that target them will continue to grow in the coming years due to a number of factors, including:
- Rise of zero-day exploitation by ransomware and data extortion groups: In 2023, zero-day exploits in MOVEit, GoAnywhere, Citrix and PaperCut were targeted significantly thanks to leak site posts.
- Continued state-sponsored exploitation attacks: A Microsoft report found instances of nation-state cyber espionage rose last year.
- Growth of “turnkey” exploit kits: Turnkey exploit kits are off-the-shelf tools that can be purchased from commercial surveillance vendors. A report by HP Wolf Security noted a surge in Excel files with DLLs infected with the cheap Parallax remote access Trojan in 2023.
Recommendations from the M-Trends report
- Maintain patch management of edge devices to prevent exploitation of known vulnerabilities.
- Take a “defence-in-depth” approach to aid in detecting evidence of zero-day exploitation.
- Perform investigations and network hunting activities if there’s suspicion of compromise and, if there is, aim to discover how attackers entered and maintained access.
- Follow security vendors’ guidance for hardening architecture to enhance defences.
- Ensure you have an incident response plan and conduct broad environmental monitoring.
- Layer network segmentation and logging with advanced EDR solutions.
- Evaluate vendors’ security practices and network requirements before deploying new hardware or software to establish a baseline for normal use.
3. Cloud environments are being targeted more often
Cloud adoption is continuously growing — Gartner predicts more than 50% of enterprises will use industry cloud platforms by 2028 — and, therefore, more attackers are turning their attention to these environments. According to CrowdStrike, there was a 75% increase in cloud intrusions in 2023 over 2022.
Mandiant analysts say attackers are targeting weakly implemented identity management practices and credential storage to obtain legitimate credentials and circumvent multifactor authentication (MFA).
SEE: UK’s NCSC Issues Warning as SVR Hackers Target Cloud Services
Mandiant observed instances where attackers gained access to cloud environments because they happened across credentials that were not stored securely. Credentials were discovered on an internet-accessible server with default configurations or had been stolen or leaked in a previous data breach and not been changed since. They also gained access using different techniques to bypass MFA, covered in more detail in the next section.
Once inside the cloud environment, the authors observed bad actors performing a number of tactics to abuse the cloud services, including:
- Using native tools and services to maintain access, move laterally or steal data: Exploiting pre-installed tools like Azure Data Factory and Microsoft Entra ID meant the adversaries could decrease their operational profile and evade detection for longer.
- Creating virtual machines (VMs) to get unmonitored access to the organisation’s cloud: When an attacker creates a VM that runs on the organisation’s cloud infrastructure, it will not have their mandated security and logging software installed on them. It can also allow for lateral movement to the on-premises network via VPN.
- Utilising the cloud’s processing power for cryptomining.
- Using open-source offensive security toolsets to survey the environment.
Recommendations from the M-Trends report
- Update employee authentication policies.
- Use phishing-resistant MFA such as certificate-based authentication and FIDO2 security keys via SMS instead of phone calls and one-time passwords.
- Implement controls that restrict access to cloud resources to only trusted devices.
4. Cyber criminals are changing tactics to bypass MFA
Now that multifactor authentication has become a standard security practice in many organisations, attackers are exploring new, creative tactics to bypass it. According to Mandiant, the number of compromises against cloud-based identities configured with MFA is increasing.
In 2023, the firm observed an increase of adversary-in-the-middle (AiTM) phishing pages that steal post-authentication session tokens and allow bad actors to circumvent MFA. In an AiTM campaign, attackers set up a proxy server that captures a user’s credentials, MFA codes and session tokens issued by the logon portal while relaying the connection to the legitimate server.
SEE: New phishing and business email compromise campaigns increase in complexity, bypass MFA
The majority of business email compromise cases Mandiant responded to in 2023 involved the threat actor circumventing the user’s MFA via AiTM. In the past, the relative complexity of setting up AiTM phishing infrastructure compared to traditional credential harvesting forms may have kept the number of these attacks low. However, there are now a number of AiTM kits and phishing-as-a-service offerings advertised in the cybercriminal underground, according to Mandiant. These products significantly lower the barrier to entry for AiTM phishing, resulting in an uptick.
Other techniques the Mandiant researchers observed attackers using to bypass MFA include:
- Social engineering attacks: For example, spear phishing emails where the target is coerced into revealing their login details on a spoofed site. The attacker then uses them to sign in on the legitimate site, which sends an MFA notification to the user who accepts. The organisation’s help desk may also be targeted with an instruction to reset a password or MFA device.
- SIM-swapping: This involves transferring a target’s phone number to a SIM card controlled by an attacker, so they can accept the MFA notification and take over an account. Mandiant observed an increase in SIM-swapping attacks in 2023.
- Password-guessing: Attackers guess the passwords to dormant or service accounts that do not have MFA set up so they can enrol their own device.
Recommendations from the M-Trends report
- Implement AiTM-resistant MFA methods and access policies that block logons based on, for example, organisation-defined locations, device management status or historical logon properties.
- Monitor authentication logs for IP addresses associated with phishing infrastructure, authentication with a stolen token or geographically infeasible logins.
5. Red teams are using AI and large language models
Red teams consist of cyber security analysts who plan and execute attacks against organisations for the purposes of identifying weaknesses. In 2023, Mandiant consultants used generative AI tools to speed up certain activities in red team assessments, including:
- The creation of initial drafts of malicious emails and landing pages for faux social engineering attacks.
- The development of custom tooling for when analysts encounter uncommon or new applications and systems.
- The research and creation of tooling in cases where environments do not fit the operational norm that can be used again and again.
Dr. Collier told TechRepublic: “The role of AI in red teaming is highly iterative with a lot of back and forth between large language models (LLMs) and a human expert. This highlights the unique contribution of both.
“AI is often well suited for repetitive tasks or fetching information. Yet, having red team consultants that understand the trade craft and possess the skills to apply context provided by LLMs in practical situations is even more important.”
AI was also used in Mandiant’s purple team engagements, where analysts must become familiar with a client’s environment from the perspective of an attacker and defender to foster collaboration between red and blue teams. Generative AI was used to help them understand the customer’s platform and its security more quickly.
SEE: HackerOne: How Artificial Intelligence Is Changing Cyber Threats and Ethical Hacking
In the report, the authors speculated on how cyber security analysts could use AI in the future. Red teams generate a substantial amount of data that could be used to train models tuned to help secure customer environments. However, AI developers will also have to find novel ways to ensure models have appropriate guardrails in place while simultaneously allowing for the legitimate use of malicious activity by red teams.
“The combination of red team expertise and powerful AI leads could result in a future where red teams are considerably more effective, and organisations are better able to stay ahead of the risk posed by motivated attackers,” the authors wrote.
Methodology
The metrics reported in M-Trends 2024 are based on Mandiant Consulting investigations of targeted attack activity conducted between January 1, 2023 and December 31, 2023.


